The digital landscape has shifted rapidly, and with it, the methods used by every modern fraudee to exploit unsuspecting individuals. As we navigate 2026, the sophistication of online scams has reached an all-time high, making personal vigilance more critical than ever. Understanding the anatomy of a scam is the first step toward building a robust defence against these evolving threats.
The Rising Tide of Digital Deception in 2026
In recent years, the frequency of cyber-attacks has surged, leaving many people vulnerable to the tactics of a professional fraudee. These individuals use advanced social engineering to manipulate emotions and gain access to private data. Consequently, the average person now faces a higher risk of identity theft than at any other point in history.
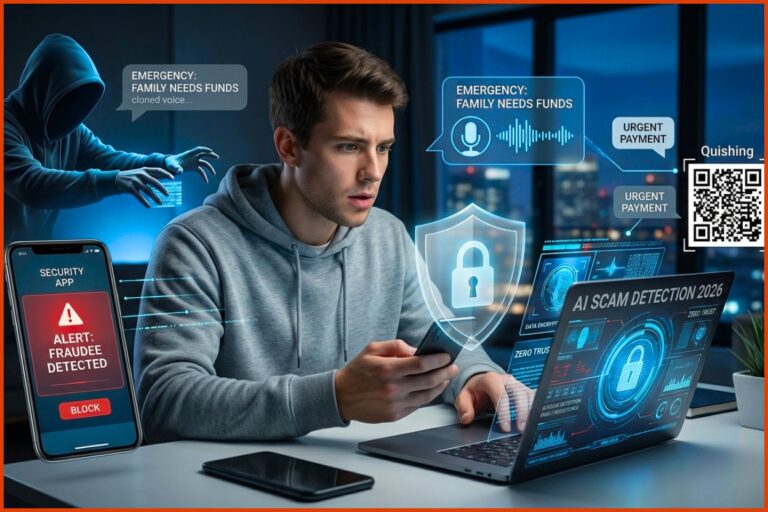
Technological advancements, while beneficial, have also enabled malicious actors to hide their tracks more effectively. For instance, artificial intelligence now allows a fraudee to create highly convincing fake personas and messages. Because these scripts look authentic, even tech-savvy users sometimes fall into these well-crafted traps. Therefore, staying informed about the latest trends in digital security is no longer optional; it is a necessity for survival in the modern age.
How the Modern Fraudee Operates
A typical fraudee does not rely on a single method to achieve their goals. Instead, they utilise a multi-layered approach that often begins with a simple, harmless-looking email or text message. This initial contact aims to build a false sense of urgency or fear, prompting the victim to act without thinking clearly.
Once the victim engages, the fraudee might direct them to a spoofed website that looks identical to a legitimate bank or government agency. At this stage, the goal is to harvest login credentials or social security numbers. In addition, many scammers now use voice-cloning technology to mimic family members, adding a terrifying layer of realism to their schemes.
Common Red Flags to Watch For
Recognising the signs of a scam can save you from significant financial loss and emotional distress. Most fraudee interactions share common characteristics, such as requests for unusual payment methods like gift cards or cryptocurrency. Furthermore, if an offer seems too good to be true, it almost certainly is a calculated lie.
Another major red flag involves unsolicited requests for sensitive information over the phone. A legitimate company will never ask for your password or full credit card details during an inbound call. However, a persistent fraudee will often pressure you to “verify” your identity immediately to avoid a supposed account suspension. By remaining calm and questioning the source, you can effectively neutralise these high-pressure tactics.
The Psychology of Social Engineering
Social engineering is the backbone of every successful fraudee operation. By targeting human psychology rather than technical loopholes, these scammers bypass even the strongest firewalls. They often play on emotions like greed, fear, or even the desire to help someone in need.
For example, a fraudee might pose as a representative from a reputable charity during a natural disaster. Because people are naturally more generous during crises, they may lower their guard and provide payment details without verifying the organisation’s legitimacy. Therefore, always conduct independent research before donating money or sharing personal details online.
Protecting Your Financial Assets
Securing your bank accounts requires a proactive strategy that goes beyond simple passwords. In 2026, every smart user should implement multi-factor authentication (MFA) on all financial platforms to block a potential fraudee. This extra layer of security ensures that even if your password is stolen, your funds remain safe.
In addition to MFA, you should regularly monitor your credit reports for any unauthorised activity. If a fraudee manages to open a new line of credit in your name, early detection is the key to minimising the damage. Setting up real-time transaction alerts on your smartphone is another excellent way to stay informed about every penny leaving your account.
Why Passwords Alone are Not Enough
While strong passwords are helpful, a determined fraudee can often bypass them through data breaches or brute-force attacks. Consequently, relying solely on a string of characters is a risky gamble in the current digital climate. Using a reputable password manager can help you generate and store complex, unique keys for every site you visit.
Furthermore, you should avoid using the same password across multiple platforms. If a fraudee gains access to one account, they will immediately try those same credentials on your email and banking sites. By diversifying your security, you create a series of walls that are much harder for any scammer to climb.
The Role of AI in Scams and Defense
Artificial intelligence has become a double-edged sword in the fight against digital crime. On one hand, a fraudee can use AI to automate phishing campaigns and create deepfake videos for extortion. On the other hand, security companies are using the same technology to detect patterns of fraudulent behaviour in real-time.
As we move deeper into 2026, AI-driven security software is becoming more accessible to the general public. These tools can scan your incoming messages and flag anything that matches the known behaviour of a fraudster. However, technology is never a perfect shield, and human intuition remains your most powerful asset when something feels “off.”
Spotting Deepfakes and Synthetic Media
Deepfakes represent a new frontier for the modern fraudee, allowing them to impersonate public figures or even your boss. These videos can look incredibly lifelike, making it difficult to distinguish between reality and fabrication. To protect yourself, look for small inconsistencies, such as unnatural blinking patterns or blurred edges around the face.
If you receive a strange video request for money, always verify the request through a secondary communication channel. Call the person directly or use a known, secure messaging app to confirm their identity. By taking this extra step, you can prevent a fraudee from using your trust against you.
Sophisticated Fraud Trends for 2026
The landscape of cybersecurity is constantly evolving to stay ahead of the next fraudee innovation. In late 2025 and 2026, we have seen a massive shift toward “Synthetic Identities.” Instead of just stealing your data, a fraudee now creates a hybrid identity by mixing real social security numbers with fake names and addresses. This allows them to build positive credit scores over months before executing a massive theft.
The Rise of “Quishing” and Smooshing
Beyond standard emails, the fraudee of 2026 uses “Quishing”—malicious QR codes placed over legitimate ones in public spaces. When you scan the code to see a menu or pay for parking, you are redirected to a site that harvests your credentials. Similarly, “Smooshing” (SIM-swap fraud) has surged, where a fraudee convinces a mobile carrier to transfer your phone number to their device, allowing them to bypass your text-based security codes.
AI-Driven Emotional Manipulation
Generative AI now allows a fraudee to sustain dozens of simultaneous “relationships” in investment scams like “Pig Butchering.” In 2026, these bots adapt their tone and personality to match your emotional triggers, making it nearly impossible to detect that you aren’t talking to a real person. Therefore, any digital relationship that quickly turns toward financial advice should be treated as a high-risk encounter.
Hardening Your Perimeter: Advanced Prevention
To truly defeat the modern fraudee, you must utilise the latest technical defences available in 2026. This includes moving toward “Phishing-Resistant MFA” such as hardware security keys. Unlike SMS codes, which a fraudee can intercept, physical keys require your actual presence to authorise a login.
Biometric Liveness Detection
Financial institutions are now adopting “Liveness Detection” to stop a fraudee from using your photo or a deepfake to access your account. These systems require you to blink, turn your head, or respond to prompts in real-time to prove you are a live human. By choosing banks and services that utilise these biometric layers, you add a significant barrier that most scammers cannot bypass.
Using Data Minimization
A fraudee can only target you if they have your data. In 2026, practising “Data Minimisation”—the act of deleting unused accounts and limiting what you share on social media—is a primary defence. The less a fraudster knows about you, the harder it is for them to craft a personalised spear-phishing attack that sounds believable.
Recovery: What to Do If the Fraudee Succeeds
If you realise that a fraudee has targeted you, the first thing to do is remain calm. Panic often leads to further mistakes, which is exactly what the scammer wants. Immediately disconnect from the internet if you suspect your computer has been compromised by malware.
Next, contact your bank and credit card companies to freeze your accounts. Inform them that a fraudee may have accessed your details so they can issue new cards and monitor for suspicious activity. Reporting the incident to national fraud centres is also a crucial step in the recovery process, as it helps law enforcement track global criminal syndicates.
Restoring Your Digital Identity
Recovering from an encounter with a fraudee can be a long and tedious process, but it is necessary for your long-term security. Start by changing every password you own, beginning with your primary email account. Because your email is often the gateway to all other services, securing it is the highest priority.
You should also notify your friends and family that a fraudee might be using your name to contact them. This prevents the scam from spreading further through your social circle. Finally, consider subscribing to an identity theft protection service that offers recovery assistance and insurance coverage for any lost funds in 2026.
The Future of Online Trust
As we look toward the end of 2026, the concept of online trust is being completely redefined. We are moving away from a system of “implicit trust” toward “zero trust,” where every interaction must be verified. While this may seem inconvenient, it is the most effective way to lock out a fraudee.
In this new environment, your digital reputation will be one of your most valuable assets. Protecting it requires constant maintenance and a healthy dose of scepticism toward every digital interaction. By following the guidelines outlined in this article, you can navigate the internet with confidence and stay one step ahead of any fraudee.
Conclusion: Staying Resilient
The battle against the digital fraudee is an ongoing struggle that requires persistence and adaptability. While technology provides the tools for these crimes, it also offers the solutions to prevent them. By combining advanced security software with a vigilant mindset, you can create a nearly impenetrable barrier around your digital life.
Remember that a fraudee relies on your silence and your haste. By slowing down, asking questions, and staying educated, you take away their power. As we move forward into 2026 and beyond, let us commit to building a safer, more secure digital world for everyone. Knowledge is the ultimate weapon against deception, and staying informed is your best defence.